SecurityTube - Learn Container Security at your own pace! With our on-demand bootcamp, use tools and techniques to audit containers, hosts, image repositories and more! Try different attacks hands-on in our labs

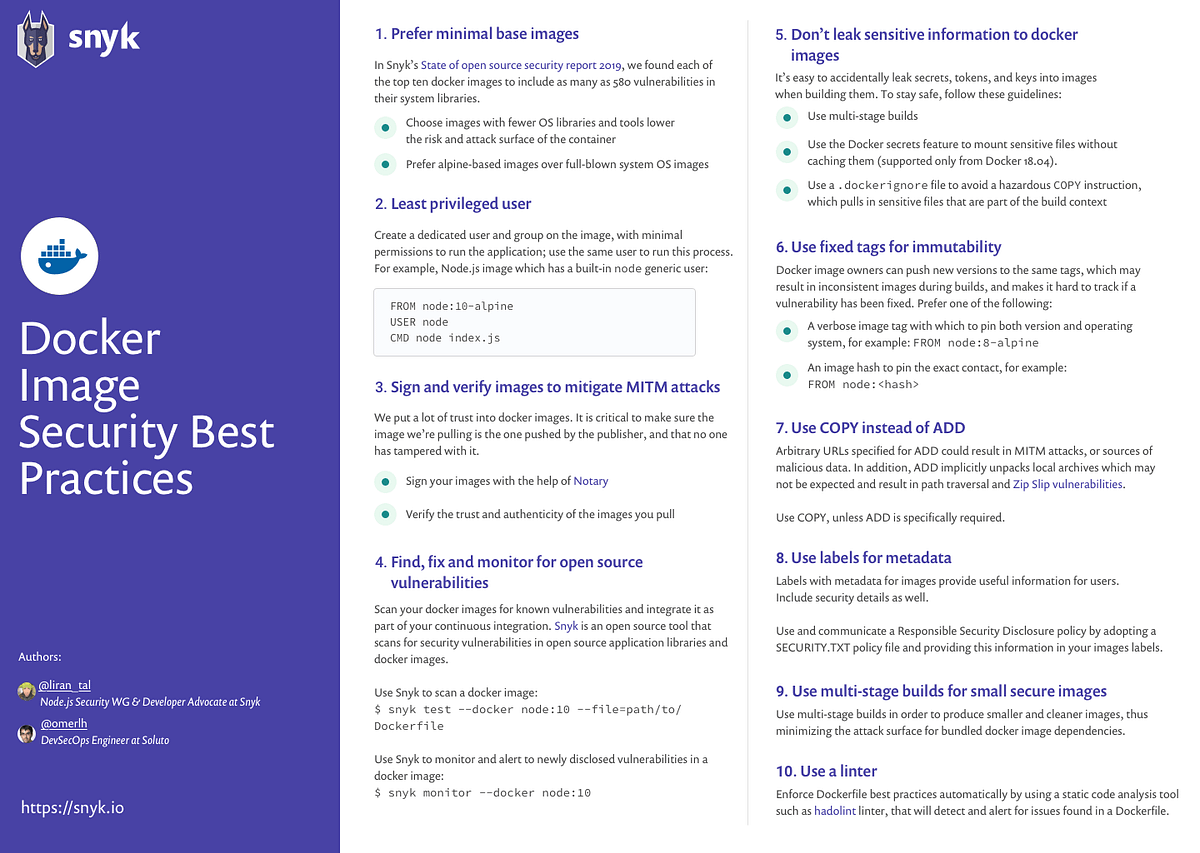
Snyk - "10 Docker image security best practices https://buff.ly/2Mnt6IN 🐳 Use a linter to enforce Dockerfile best practices 🐳 Sign and verify images to mitigate MITM attacks 🐳 Use COPY instead of
Technical Report on Container Security (V)-3 - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.
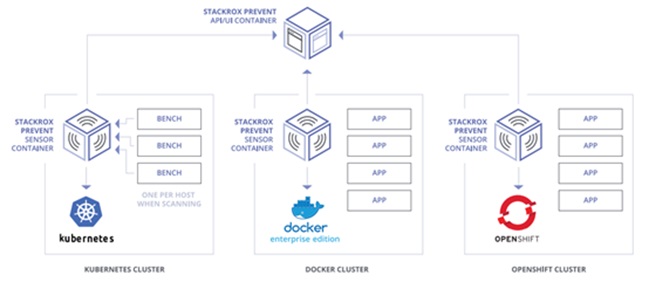
2 Widespread Attacks on Your Containerized Environment and 7 Rules to Prevent it. | by Boris Zaikin | ITNEXT
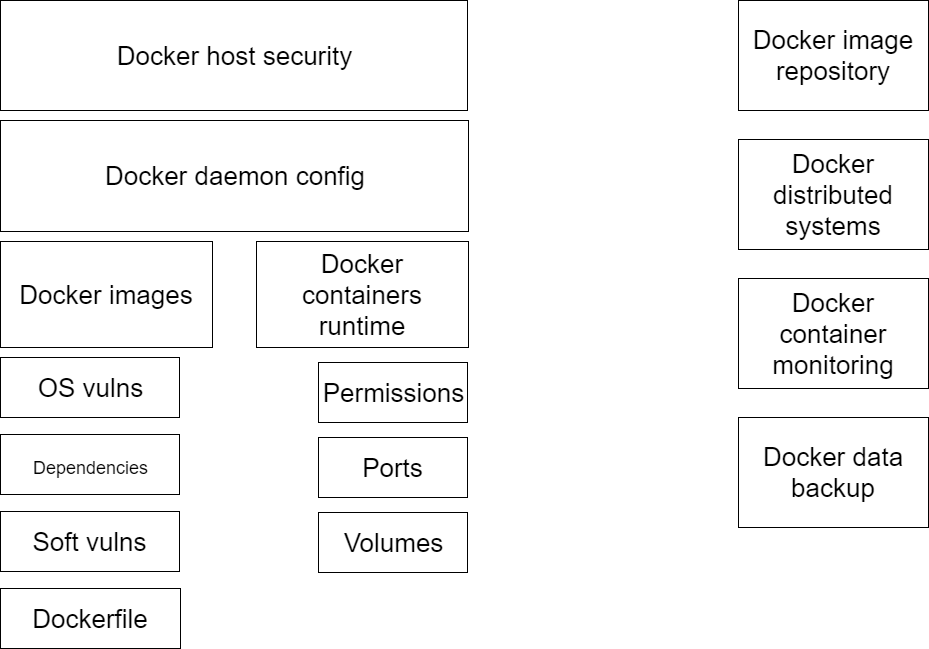
Frequently Forgotten Docker Security Practices | Administration of servers and technical support of sites